By David Graham, Vice President, Global Brand Protection, Authentix
The anti-counterfeiting industry plays an increasingly important role in protecting brand owners by helping to prevent the financial losses and dangers to their consumers caused by counterfeit products. As a leader in brand protection, Authentix prioritizes the protection of our client’s products from fraud and imitation, preventing revenue loss and maintaining the trust of their consumers.
To provide complete brand protection and support to our clients, it is essential that we understand their customer’s issues and needs. Developing a comprehensive brand protection program relies on our fundamental understanding of their consumers so we can develop protection strategies that effectively mitigate risks and provide quality services. Doing so will build confidence and enhance satisfaction for our clients and their customers.
The Real Impact of Counterfeiting for Consumers
Understanding our client’s customers is essential in recognizing the impact of counterfeit products on their lives. Counterfeit products are typically of low quality and pose a higher risk of health issues. They often lack protective features, resulting in significant harm to end consumers.
For example, counterfeit pharmaceutical products can cause users severe harm or even death. Similarly, the use of counterfeit automotive parts can lead to serious injuries or fatal accidents on the road. The impact of counterfeit products extends beyond monetary losses for brand owners, emphasizing the importance of preventing counterfeit products from entering the market.
By better understanding the true impact of counterfeit products on our clients’ customers effective strategies can be developed, and the necessary preventive measures taken. Through improved cause-effect analysis, Authentix can better identify the probability of a product becoming compromised and explore appropriate security solutions to implement and combat these risks.
Designing Brand Protection Strategies That Attract Consumers
Authentix prioritizes the end customer experience to offer relevant and practical solutions that effectively address their needs. By understanding customer’s preferences and purchasing habits, Authentix can design customized brand protection strategies targeted at the appropriate markets. This involves identifying prevalent counterfeiting issues in specific markets and developing practical measures to promptly detect and prevent these issues, thereby safeguarding the brand from potential damage.
Understanding client and end-customer needs and preferences is an ongoing process that necessitates constant monitoring and updating. This ensures the deployment of the most suitable brand protection solution that effectively caters to the target customers. Through continuous assessment and collaboration with our clients, we can adjust and modify strategies to align with market changes and emerging consumer issues. Being adaptable and flexible in our approach and methodology is a fundamental value at Authentix, ensuring client satisfaction and security are upheld.
Retaining & Restoring Consumer Trust
Understanding the end customer experience also offers the advantage of protecting and enhancing brand reputation. Counterfeit products can severely undermine customer trust in the brand(s). By implementing effective anti-counterfeit measures and fulfilling our commitment to brand protection, our clients can preserve and strengthen their customer’s faith and confidence. This is especially crucial for companies that have encountered potential counterfeit incidents and need to restore trust among their core clientele for sustained long-term success.
Improving Revenue
Authentix places significant importance on end consumers, which directly impacts our client’s financial success. Authentix provides effective preventive brand protection measures that mitigate revenue loss by proactively addressing potential issues that may affect customers. Our efforts ensure the proper implementation of specialized brand protection programs and anti-counterfeit measures for our clients.
When customers perceive a company’s genuine dedication to product safety and attentiveness to their needs and concerns, they are more likely to remain loyal and make future purchases. Retaining satisfied and trusting customers is typically more cost-effective and less time-consuming than acquiring new customers.
Brand Protection Programs Promote Confidence
Understanding the issues and needs of our client’s customers is a fundamental aspect of a successful brand protection partnership at Authentix. We strive to safeguard our clients’ products from compromise, which can have significant financial implications and potentially harm consumer health, impacting brand credibility.
Authentix is committed to raising awareness of the crucial role that comprehensive brand protection programs play in our clients’ continued success and to providing quality and trusted brand protection solutions and services that produce excellent results. Understanding our client’s end consumer is central to our operations, ensuring optimal outcomes are achieved.
Ready to Learn More?
About Authentix
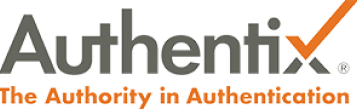
As the authority in authentication solutions, Authentix brings enhanced visibility and traceability to today’s complex global supply chains. For over 25 years, Authentix has provided clients with physical and software-enabled solutions to detect, mitigate, and prevent counterfeiting and other illicit trading activity for currency, excise taxable goods, and branded consumer products.
Through a proven partnership model and sector expertise, clients experience custom solution design, rapid implementation, consumer engagement, and complete program management to ensure product safety, revenue protection, and consumer trust for the best-known global brands on the market. Contact us now to see what we can do for your brand.
David Graham, Vice President, Global Brand Protection for Authentix
With over thirty years of experience managing the extensive supply chains of numerous global retail giants throughout Europe, Africa, Australia and Asia, David brings a vast amount of expertise and knowledge to the Authentix Brand Protection team.
Having worked closely with Brands over the years—living and working in these continents—David is able to bring a better understanding and appreciation of what Brands are looking for to better secure their products in the hectic world of global brand protection and anti-counterfeiting.
To learn more about our brand protection solutions and how we can help you, please email David at David.graham@authentix.com.





 To expand its capabilities in digital brand protection for brand owners, Authentix has recently acquired Strategic IP Information Pte Ltd (SIPI), a leading online brand and content rights protection service.
To expand its capabilities in digital brand protection for brand owners, Authentix has recently acquired Strategic IP Information Pte Ltd (SIPI), a leading online brand and content rights protection service.