Counterfeiting, smuggling, diversion, and infringement — collectively known as illicit trade, — continues to be a growing global problem for businesses and consumers. With the increasing volume of counterfeit goods trafficked across the globe and seeping into multiple supply chains, a well-strategized brand protection program is more essential than ever to shield what matters most to businesses – customers, brand identity, reputation, and revenue.
By Type: Articles
Verifying Sustainable Fuels
|Navigating Brand Protection Strategies For Your Business
|By the Authentix Brand Protection team
Back in the 1700’s Ben Franklin was an early innovator of printing techniques that made American paper currency harder to counterfeit. Some of his security features included watermarks, imprints of leaves, and other difficult-to-reproduce features that helped citizens distinguish real bills from illegal copies.
Since then, security feature graphics have of course evolved, but many of these early anti-counterfeit security features have stood the test of time. There are dozens of secure printing, digital authentication, and online protection technologies that can help your brand keep products secure and prevent counterfeiting. Here’s a breakdown of the top security and authentication technologies that might be right for your brand protection needs:
Physical Security Features
Having a multi-layered physical security authentication solution is important to protect your products. If a counterfeiter figures out how to print one security feature like UV, you still have more layered features to verify if the product is indeed yours. There are a wide range of physical security options available, from obvious and overt like holographic images and color shifting inks, to invisible covert and forensic security which are impossible to detect without the proper tools.
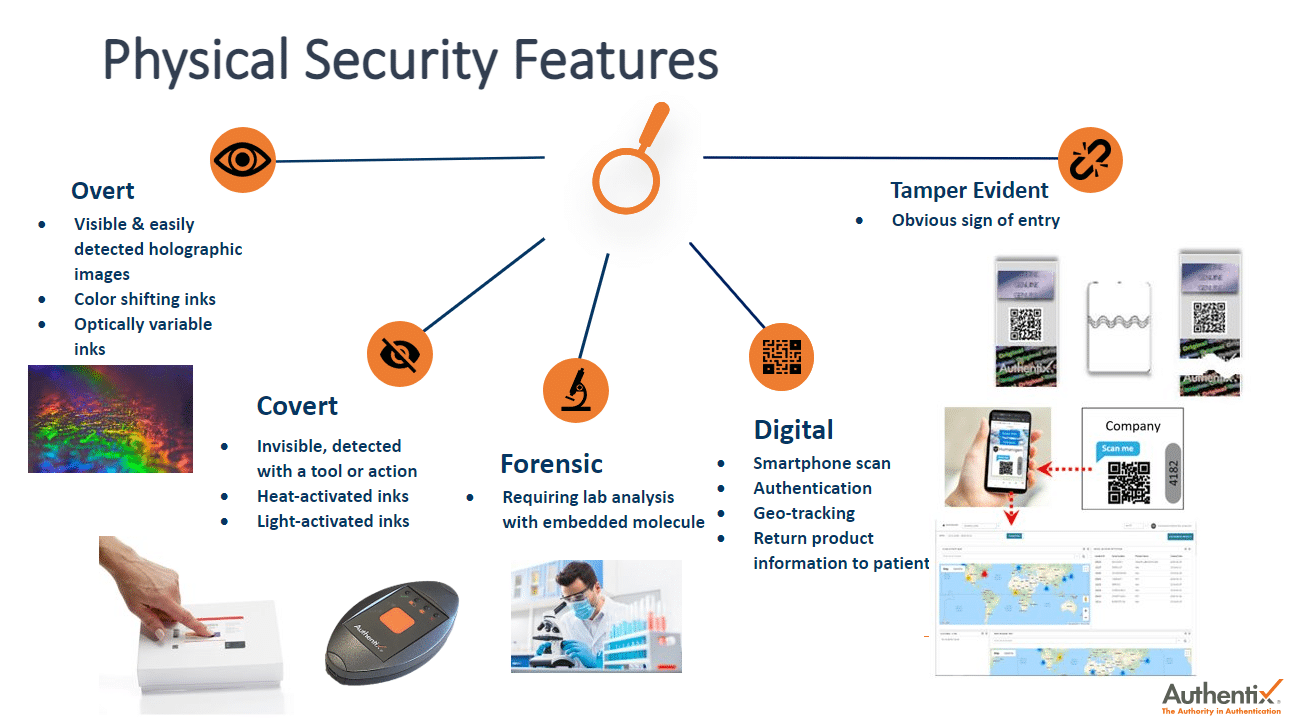
Some popular physical security examples include:
- Tamper evident packaging – labels, stickers, or seals that when opened or tampered with, provide immediate evidence that the product has been compromised.
- Chemical and physical markers – can be hidden from consumers and counterfeiters and can only be seen with specific detectors that are calibrated to a specific wavelength to verify authenticity.
- QR Codes – can now be scanned without the need for an app, using a smartphone camera that directs consumers to a webpage to authenticate the product and then introduces the consumer to another webpage where they can register their warranty, learn more about the product and even suggest other complementing products.
Physical security features will continue to evolve and remain an important part of your brand protection strategy. Future trends in physical security include new nanoprint technologies, printed electronics, and revolutionary inventions in digital printing. It is anticipated that these and many more will become the standard for high security printing.
Digital Authentication
Digital product authentication is a brand protection strategy that works by adding a unique digital identifier to your product. This allows your company to track the lifecycle of products, identify where transactions are taking place, and provides data analytics and insight into your products and customers. Unique QR codes on each product can be scanned by inspectors along the supply chain to ensure authenticity, as well as by end customers at the point of sale. Consumers can instantly authenticate their products and your brand can engage customers by serving relevant offers and information.
For example, a well-known spirits company was facing counterfeits across China, resulting in loss of brand loyalty, consumer trust and revenue. Authentix helped them implement a multi-layered authentication solution using covert and overt features. One of the solutions implemented was a QR code featuring a digital consumer engagement experience as well as authentication verification. The result was 90 million bottles with unique identifiers that could be tracked through the supply chain, allowing the company to detect and shut down over 150 counterfeiting locations including warehouses, retail shops and print shops.
Online Brand Protection
The rise in online sales has been unfortunately accompanied by the rise in counterfeiting on online marketplaces, social media platforms, and websites. When looking for an online brand protection services provider, it is important to ensure their scanning software is proprietary and not provided by a third party. This gives you more control and security and makes it easier to do takedowns on social media where counterfeiters can advertise for a few hours at a time to targeted audiences. You should also ensure that your protection partner has the ability and resources to scan webpages and marketplaces, social media platforms, e-commerce apps, messaging apps like WeChat, payment sites, and the dark web for infringing content and listings.
It is also important for your online brand protection partner to have global marketplace coverage to allow you to do test purchases and verify product authenticity around the world. AI and machine learning capabilities can also give you actionable insights that lead to in-person shut downs and allow local law enforcement to conduct raids.
Following is a good example of one of Authentix’s clients using online brand protection technology to secure their brand:
This case is very similar to most companies that sell their products online. The company was a highstreet fashion brand that had a problem with lookalike and copycat products, posing a threat to their brand reputation and a decrease in sales. After Authentix implemented various image recognition tools that analyze and compare images against known logos and patented designs, test purchases were made and it was detected that the products were indeed infringements. The success rate from online enforcement was 98% and over 300 raids were then conducted, resulting in 8 civil litigation cases.
Evaluating Your Brand Protection Needs
Security should be integrated into your brand protection solution design from day one, not just as an afterthought. Early evaluation helps your brand with packaging design and product launches further down the road. Conducting a brand risk assessment helps determine in which markets your company is having counterfeiting issues and can help you gauge which type of security solution or solutions are the best fit for your situation. Having security technologies that give customers peace of mind the product they are purchasing is authentic, can be a great strategic advantage as your competitors struggle to add security to their products once they suffer the effects of counterfeits. Security should be a priority for long-term success so that your weak points don’t become susceptible to counterfeiters.
Authentix Customized Brand Protection Solutions
Authentix’s team of brand protection experts is ready to help your company every step of the way to protect your products with the latest and greatest security technology capabilities. Here are just some of the things you can expect when you work with our brand protection specialists:
- Assessment and advisory services
- Defining the gaps between your current practices and industry leading practices
- Specific recommendations for improvement
- Assistance with process implementation
- Forensic product analysis services
- Risk and vulnerability assessment
- Simulated detection by third parties
- Identification of possible materials used for security feature replication
- Prototype development services
- Product and packaging prototypes that incorporate security features designed specifically for you
- Implementation services
- Help managing the deployment of Anti-Counterfeiting Program technology in your facility
Contact Authentix today to learn more about how our brand protection strategies can help maintain your brand’s integrity in the global marketplace.
About Authentix
As the authority in authentication solutions, Authentix brings enhanced visibility and traceability to today’s complex global supply chains. For over 25 years, Authentix has provided clients with physical and software-enabled solutions to detect, mitigate, and prevent counterfeiting and other illicit trading activity for currency, excise taxable goods, and branded consumer products. Through a proven partnership model and sector expertise, clients experience custom solution design, rapid implementation, consumer engagement, and complete program management to ensure product safety, revenue protection, and consumer trust for the best known global brands on the market. Headquartered in Addison, Texas USA, Authentix, Inc. has offices in North America, Europe, Middle East, Asia, and Africa serving clients worldwide.
Understanding the SHOP SAFE Act and How to Safeguard Your Brand
|In the digital age, a brand’s reputation is a crucial asset and one of the greatest threats a brand faces is counterfeiting. Whether it’s a popular weight-loss drug like semaglutide or designer apparel, the counterfeit market is thriving and costing brands billions of dollars every year. The impact goes far beyond financial losses; it puts consumer health and safety at risk. Due to the rise in harmful counterfeit products across a variety of industries, the US Senate Judiciary Subcommittee on Intellectual Property introduced the Stopping Harmful Offers on Platforms by Screening Against Fakes in E-Commerce (SHOP SAFE) Act. The SHOP SAFE Act is legislation aimed at reducing the volume of counterfeit sales online. It includes provisions such as holding platforms accountable for counterfeits that endanger consumer health and safety, requiring them to verify and display sellers’ identity and contact information, and terminating the accounts of repeat infringers.
Criticisms to the SHOP SAFE Act have led to the realization among lawmakers and courts that striking a balance between safe harbor principles and responsibilities is necessary, given the health and safety risks associated with counterfeit products.
The Impact of Widespread Counterfeit Pharmaceuticals
The surge in counterfeit pharmaceuticals such as semaglutide, better known under the commercial brand name Ozempic, has resulted in consumers falling seriously ill after purchasing these fake products online. After a huge surge in demand for the drug in 2023, pharmacies have struggled to keep it in stock and counterfeiters have taken advantage of the lack of availability by flooding the internet with fake semaglutide. Healthcare agencies in the UK have reported multiple cases of consumers falling seriously ill after purchasing counterfeit semaglutide online. Recently, a BBC investigation similarly uncovered cases of consumers buying counterfeit semaglutide pens from sellers on Instagram, WhatsApp and TikTok, with some ending up being hospitalized. Another example comes from Austria where several patients injected with suspected counterfeit semaglutide were hospitalized after suffering from hypoglycemia and seizures. This reality underscores the importance of the SHOP SAFE Act and why brand protection is no longer a choice but a necessity for businesses and consumer protection.
To dig deeper into the extent of the counterfeit semaglutide market, Authentix Online Brand Protection (OBP) scanned multiple platforms and found several suspicious listings of semaglutide across social media and messaging apps and online marketplaces.
In the absence of a detailed investigation, it is difficult to establish which of these products are counterfeit and governments and the industry would benefit from investigating such listings in greater detail. For example, many suspicious listings found by Authentix OBP contained clickbait hashtags like #weightloss and #ozempic. These could serve as a starting point for an investigation. Further, selling even genuine semaglutide without a prescription is an offence in most jurisdictions. Listings of such a nature should automatically be taken down by platforms without insistence on documentation such as IP registration certificates. Similarly, parallel imports should also be treated by platforms as serious cases, not least because these products may be tampered with and may also contain literature in languages not native to the country of sale. The same goes for a significant reduction in retail price — a common tactic employed by rogue sellers to lure consumers. To truly bust the counterfeit semaglutide market, however, will require a sustained cross-border effort that targets known high-risk marketplaces and platforms, and eventually results in physical investigations and enforcement actions.
The Importance of Counterfeit Prevention
Authentix OBP recommends brands check a wide range of sites for infringing products as new listings and new marketplaces for counterfeit goods pop up every day. Between constant monitoring of online marketplaces and e-commerce sites, implementing cutting-edge technology to detect infringing listings, and expert-led takedowns of counterfeit listings, a full online brand protection solution helps brands protect their company and customers from counterfeiters.
The SHOP SAFE Act places an obligation on companies to protect their consumers, and Authentix OBP equips brands with the power and tools to do so – a perfect synergy for safeguarding your brand’s integrity and keeping consumers safe.
About Authentix Online Brand Protection
Authentix provides some of the world’s most recognizable brands with sophisticated online brand protection tools and services to address a broad range of online infringement and counterfeit risks. From global online surveillance and enforcement, online investigations and site takedowns, target verification, and even offline investigations, Authentix helps major brands proactively reduce the threat of counterfeit products being sold online. Our online brand protection solutions combine cutting-edge technological tools and expert analysis to reduce infringements for our clients on online marketplaces, social media platforms, and websites by up to 90%.
Want to see what Authentix OBP can do for your company? Our team is committed to working with you, understanding your unique challenges and requirements, and providing tailored solutions that best fit your industry and the unique challenges your brand faces that make a tangible difference to your brand. Schedule a consultation with one of our brand protection experts to learn more.
Q&A on Intellectual Property Protection & Enforcement
|By Bharat Kapoor, Vice President, Online Brand Protection, Authentix
The International Anti-Counterfeiting Coalition (IACC) recently asked our VP of Online Brand Protection, Bharat Kapoor, his thoughts on intellectual property protection and enforcement and here’s what he shared:
What are the top 2 challenges in IP enforcement you see affecting your industry over the next year?
On the one hand, as online sales occur in an omni-channel environment, brands need to focus on collecting and analyzing the right set of data to make connections and take down infringing distribution channels collectively. On the other hand, ecommerce marketplaces and social media are making it increasingly difficult for brands to access sellers on their platform, with search and enforcement tools becoming less effective at tackling the range of issues online. Brand protection teams need to address these challenges by having targeted strategies supported with data and insights to deliver results and to avoid being overly reliant with on-ground investigators.
Can you provide your top 2 best practices for protecting IP?
 First, it is important to have registered IP rights and the ability to authenticate products efficiently. Second, the ability to collect and analyze high-quality data and manage a range of enforcement activity efficiently across hundreds of marketplaces globally is the most important factor in protecting IP. Authentix’s online brand protection solution and service platform gives our clients the ability to find and connect activities on a range of issues across ecommerce channels and further enables our global services team to manage these brand protection activities at scale. We also have active channels of communication with marketplaces to continuously address online threats collaboratively, and actively call out their lack of cooperation publicly.
First, it is important to have registered IP rights and the ability to authenticate products efficiently. Second, the ability to collect and analyze high-quality data and manage a range of enforcement activity efficiently across hundreds of marketplaces globally is the most important factor in protecting IP. Authentix’s online brand protection solution and service platform gives our clients the ability to find and connect activities on a range of issues across ecommerce channels and further enables our global services team to manage these brand protection activities at scale. We also have active channels of communication with marketplaces to continuously address online threats collaboratively, and actively call out their lack of cooperation publicly.
What hobbies or causes are you passionate about?
We are deeply committed towards sustainability and Authentix Inc. has funded numerous environmental and educational projects in Africa, South America, and many other communities we serve. We have also implemented best practices on sustainability within the global organization. We have been following industry discussions on upcycling of counterfeit goods, and we have supported our clients in building strategies in certain countries. We are passionate about using our skills to support causes that positively impact the environment and conducting investigations into issues such as the illegal trafficking of birds and wildlife. Delivering results on projects such as these reenergizes me and our team to continue to fight against illegal activities online.
Want to learn more about how Authentix can help protect against intellectual property infringement? Schedule a consultation with our brand protection experts today.
Bharat Kapoor, Vice President, Online Brand Protection, Authentix
Formerly the CEO of Strategic IP Information Pte, now a part of Authentix, Bharat has been focused on building effective global brand protection programs for over 250 brands across sectors such as fashion, FMCG, pharma, cosmetics, sporting goods wines, and spirits. He has led the development of the best-in-class machine learning-based online brand protection technology and developed effective global teams to investigate counterfeiting and piracy on the ground in China, Asia, and Latin America. Bharat Kapoor has a B.A. Honors from the University of Technology, Sydney. Prior to joining SIPI, he was an Associate Director at Ernst & Young India, where he led the business development and advisory services program for companies operating in the media, e-commerce, and advertising sectors.
Digital Avatars and the Perils of IP Infringement
|By Bharat Kapoor, Vice President, Online Brand Protection, Authentix
One of the visible recent trends online has been the rise of realistic, AI-generated celebrity avatars. These may take myriad forms (from 3D animations to chatbots) and are generated using a variety of AI technologies (including publicly available apps like Silver Studio and Lensa). Many well-known figures have jumped on the bandwagon and commercialized their AI avatars through strategic partnerships with brands and social media platforms — from Snoop Dogg and Kendall Jenner (partnering with Meta) to Slovenian NBA star Luka Dončić (who has commissioned a digital doppelgänger that can interact with fans on TikTok). In South Korea, an entire K-Pop band “Eternity” has been artificially created by a technology company, using deepfake and motion capture technology.
Legal Precedents Protecting Likeness
The emerging trend of digital avatars brings with it several potential intellectual Property (IP) risks. These risks include false endorsement (by using an avatar to promote an unlicensed product); reputational damage (by using deepfake technology to make a celebrity appear to say or do something unsavory); or straightforward copyright infringement (by copying videos and images, which could then be commercially exploited in various ways, from use in NFTs to social media pages). There are judicial precedents on personality rights worldwide, including in cases preceding the internet, that can prevent wrongful appropriation. For example, in Midler v Ford Motor Co (1988), the singer Bette Midler sued Ford for using a “sound-alike” singer to imitate her voice in a series of commercials. The US Court of Appeals for the Ninth Circuit ruled in her favor, under a California tort statute that prohibited the use of a person’s “name, voice, signature, photograph or likeness, in any manner.” Subsequent cases in the US, UK, and many other countries, have reaffirmed the decision to protect public figures from unauthorized use of their image, likeness, or voice in advertisements or endorsements without their permission. Among recent cases, in April 2023, the Chinese Hangzhou Internet Court ruled that the image and related videos of “Ada”, an AI character created by a Chinese tech company, enjoyed protection under Chinese copyright law. The court further ruled that the defendant had engaged in unfair competition by using Ada’s images and videos to promote products on Douyin.
How To Protect Against Digital Infringement
While international precedents are undoubtedly helpful in protecting digital avatars and personality rights globally, at least two significant challenges remain. First, detecting the misuse of avatars can be difficult in cases where such misuse is widespread (often because rights owners have allowed the problem to fester). Such cases may require scanning hundreds of pages and sending an equivalent number of takedown requests. Second, stemming from the first, not all platforms may be receptive to cooperating with takedown requests. For example, relying solely on case law from foreign jurisdictions, in the absence of a domestic statute clearly recognizing personality rights, may not sway certain platforms to remove infringing products. Some platforms also insist on documentation and certain IP offices may not issue certificates explicitly recognizing personality rights. It is also plausible that some misappropriated avatars may deliberately include dissimilarities in order to resist takedowns. Platforms may also construe certain uses as falling within the realm of fair use, especially if such use is in contexts that are not outrightly commercial. These problems can be suitably addressed by using advanced IP surveillance software, supplemented by a team of experts handling the complex takedown requests, escalating issues to executives, and supplying robust legal reasoning. In the end, the misappropriation of avatars is still a relatively recent problem, and the attitudes of platforms are yet to be discerned. Nevertheless, experience shows that the above problems are highly plausible, which should cause rights owners to be both vigilant and realistic on matters of enforcement.
Authentix Online Brand Protection
Authentix provides some of the world’s most recognizable brands with sophisticated online brand protection tools and services to address a broad range of online infringement and counterfeit risks. From global online surveillance and enforcement, online investigations and site takedowns, target verification, and even offline investigations, Authentix helps major brands to proactively reduce the threat of unauthorized likeness use and IP infringement. Our online brand protection solutions combine cutting-edge technological tools and expert analysis to reduce infringements for our clients on online marketplaces, social media platforms, and websites by up to 90%. If you’re curious how Authentix Online Brand Protection can help protect against intellectual property infringement, schedule a consultation with our brand protection experts today.
Bharat Kapoor, Vice President, Online Brand Protection, Authentix
Formerly the CEO of Strategic IP Information Pte, now a part of Authentix, Bharat has been focused on building effective global brand protection programs for over 250 brands across sectors such as fashion, FMCG, pharma, cosmetics, sporting goods wines, and spirits. He has led the development of the best-in-class machine learning-based online brand protection technology and developed effective global teams to investigate counterfeiting and piracy on the ground in China, Asia, and Latin America. Bharat Kapoor has a B.A. Honors from the University of Technology, Sydney. Prior to joining SIPI, he was an Associate Director at Ernst & Young India, where he led the business development and advisory services program for companies operating in the media, e-commerce, and advertising sectors.
Understanding Our Clients’ Customers is Critical to a Successful Brand Protection Program
|By David Graham, Vice President, Global Brand Protection, Authentix
The anti-counterfeiting industry plays an increasingly important role in protecting brand owners by helping to prevent the financial losses and dangers to their consumers caused by counterfeit products. As a leader in brand protection, Authentix prioritizes the protection of our client’s products from fraud and imitation, preventing revenue loss and maintaining the trust of their consumers.
To provide complete brand protection and support to our clients, it is essential that we understand their customer’s issues and needs. Developing a comprehensive brand protection program relies on our fundamental understanding of their consumers so we can develop protection strategies that effectively mitigate risks and provide quality services. Doing so will build confidence and enhance satisfaction for our clients and their customers.
The Real Impact of Counterfeiting for Consumers
Understanding our client’s customers is essential in recognizing the impact of counterfeit products on their lives. Counterfeit products are typically of low quality and pose a higher risk of health issues. They often lack protective features, resulting in significant harm to end consumers.
For example, counterfeit pharmaceutical products can cause users severe harm or even death. Similarly, the use of counterfeit automotive parts can lead to serious injuries or fatal accidents on the road. The impact of counterfeit products extends beyond monetary losses for brand owners, emphasizing the importance of preventing counterfeit products from entering the market.
By better understanding the true impact of counterfeit products on our clients’ customers effective strategies can be developed, and the necessary preventive measures taken. Through improved cause-effect analysis, Authentix can better identify the probability of a product becoming compromised and explore appropriate security solutions to implement and combat these risks.
Designing Brand Protection Strategies That Attract Consumers
Authentix prioritizes the end customer experience to offer relevant and practical solutions that effectively address their needs. By understanding customer’s preferences and purchasing habits, Authentix can design customized brand protection strategies targeted at the appropriate markets. This involves identifying prevalent counterfeiting issues in specific markets and developing practical measures to promptly detect and prevent these issues, thereby safeguarding the brand from potential damage.
Understanding client and end-customer needs and preferences is an ongoing process that necessitates constant monitoring and updating. This ensures the deployment of the most suitable brand protection solution that effectively caters to the target customers. Through continuous assessment and collaboration with our clients, we can adjust and modify strategies to align with market changes and emerging consumer issues. Being adaptable and flexible in our approach and methodology is a fundamental value at Authentix, ensuring client satisfaction and security are upheld.
Retaining & Restoring Consumer Trust
Understanding the end customer experience also offers the advantage of protecting and enhancing brand reputation. Counterfeit products can severely undermine customer trust in the brand(s). By implementing effective anti-counterfeit measures and fulfilling our commitment to brand protection, our clients can preserve and strengthen their customer’s faith and confidence. This is especially crucial for companies that have encountered potential counterfeit incidents and need to restore trust among their core clientele for sustained long-term success.
Improving Revenue
Authentix places significant importance on end consumers, which directly impacts our client’s financial success. Authentix provides effective preventive brand protection measures that mitigate revenue loss by proactively addressing potential issues that may affect customers. Our efforts ensure the proper implementation of specialized brand protection programs and anti-counterfeit measures for our clients.
When customers perceive a company’s genuine dedication to product safety and attentiveness to their needs and concerns, they are more likely to remain loyal and make future purchases. Retaining satisfied and trusting customers is typically more cost-effective and less time-consuming than acquiring new customers.
Brand Protection Programs Promote Confidence
Understanding the issues and needs of our client’s customers is a fundamental aspect of a successful brand protection partnership at Authentix. We strive to safeguard our clients’ products from compromise, which can have significant financial implications and potentially harm consumer health, impacting brand credibility.
Authentix is committed to raising awareness of the crucial role that comprehensive brand protection programs play in our clients’ continued success and to providing quality and trusted brand protection solutions and services that produce excellent results. Understanding our client’s end consumer is central to our operations, ensuring optimal outcomes are achieved.
Ready to Learn More?
About Authentix
As the authority in authentication solutions, Authentix brings enhanced visibility and traceability to today’s complex global supply chains. For over 25 years, Authentix has provided clients with physical and software-enabled solutions to detect, mitigate, and prevent counterfeiting and other illicit trading activity for currency, excise taxable goods, and branded consumer products.
Through a proven partnership model and sector expertise, clients experience custom solution design, rapid implementation, consumer engagement, and complete program management to ensure product safety, revenue protection, and consumer trust for the best-known global brands on the market. Contact us now to see what we can do for your brand.
David Graham, Vice President, Global Brand Protection for Authentix
With over thirty years of experience managing the extensive supply chains of numerous global retail giants throughout Europe, Africa, Australia and Asia, David brings a vast amount of expertise and knowledge to the Authentix Brand Protection team.
Having worked closely with Brands over the years—living and working in these continents—David is able to bring a better understanding and appreciation of what Brands are looking for to better secure their products in the hectic world of global brand protection and anti-counterfeiting.
To learn more about our brand protection solutions and how we can help you, please email David at David.graham@authentix.com.
Can a Company Be Truly Sustainable Without Considering How to Prevent Counterfeiting?
|By Mike Consterdine, Brand Account Development Manager
Globally, many companies have committed to the fight against plastic pollution, with manufacturers changing components and materials to produce more recyclable packaging. The time and investment put into this sustainability goal is also a balancing act with businesses becoming carbon neutral.
However, a sometimes forgotten consideration is that counterfeit products entering the supply chain may lack sustainable materials and are often unsafe and non-compliant. In this light, an essential component of sustainability efforts is to prevent counterfeiting.
The main motivation for those conducting illicit trade is financial gain. Therefore, there is an overwhelming argument that sustainability is not considered in the manufacturing, distribution and sale of counterfeit products. Counterfeiters manufacture these goods in factories that are often unregulated and include cheaply sourced and substandard materials that are not only harmful to workers but also contribute to the pollution of the environment.
So the question is, can companies truly achieve sustainability while at the same time not considering or having a plan to remediate counterfeit goods? We’ll see that sustainability and counterfeiting prevention go hand-in-hand.
The Impact of Counterfeiting
While it’s well-known that counterfeiting and intellectual property infringement supports organized crime, there are also other societal impacts to consider:
- Illicit trade rings traffic people across borders for exploitative labor, often in abhorrent conditions with little or no compensation.
- Across multiple sectors, including apparel, consumer goods, cosmetics, electronics and pharmaceuticals, counterfeit products have been proven to contain hazardous and toxic elements. When those products come into contact with a person or are consumed, they can be harmful or even fatal.
- Counterfeit or non-compliant products may find their way into legitimate manufacturing and distribution channels, compromising supply chain integrity. This results in companies being unable to prove that the product or process adheres to company sustainability statements and practices.
- When counterfeit products are seized, there is an opportunity to reuse or recycle them. However, de-labeling a branded item is not always possible as this process can also be costly, and some product materials are unsafe to reuse. In these circumstances, the products will be destroyed by court order, impacting the environment with further waste and pollution.
The ability to prevent counterfeiting substantially reduces all these risks.
How to Prevent Counterfeiting
There are many ways companies can prevent counterfeiting. First, they should conduct a comprehensive review of intellectual property rights and supply chain channels. This process will provide insight into the strengths and weaknesses of company processes and their IP portfolio. The results allow efficient and effective decision-making by legal, regulatory and enforcement teams and support sales, marketing and operational divisions.
The next essential step, even if the company has an in-house brand protection specialist, is collaborating with key partners. These partners can include regional enforcement teams, online brand protection service providers and those who are experts in securing products through authentication and traceability solutions.

An online brand protection company can assess the market while providing an overall view of the extent of the IP infringement problem, whether that be in counterfeit, design or copyrights. Engaging a third-party provider for brand protection services assists in time management. They also can conduct online takedowns and provide actionable intelligence for prioritizing offline targets.
By applying a unique and secure identifier to a product or packaging, a product can be authenticated or tracked through its lifecycle, with all data on the product stored in a cloud-based platform for various business functions. Consumers or field investigators also can immediately authenticate a product by scanning the identifier via an app, a forensic reader or a mobile/cellular device.
By implementing these strategies, a company can mitigate its risk of counterfeiting, diversion and non-compliant products entering the legitimate supply chain.
Return on Investment
Brand protection can be seen as a cost center. But a return on investment can be determined by increased consumer confidence through fewer customer returns, higher sales driven by the removal of infringing online content and offline target prioritization. Brand protection can also help avoid costly product recalls, which will likely increase emissions, representing another link between preventing counterfeits and sustainability.
Implementing secure brand protection technologies can also lead to more efficient processes and less waste, supporting company sustainability initiatives.
Combining Sustainability and Counterfeiting Prevention
While counterfeiting can be deemed a byproduct of a successful business, it can irreparably damage a brand’s reputation with customers and the general public. It also invites questions regarding what the intellectual property rights holder is doing to prevent unregulated, often harmful, illegal practices.
Corporate social responsibility is often seen as a buzzword. But, when it comes to consumer trust and sustainability statements, it is imperative to consider all factors. Reviewing component sourcing, manufacturing processes, policies and regulations is only the start to increasing sustainability.
Brand protection, online and offline, is more than “stopping the fakes.” It’s also about protecting reputation, human life and the environment.
Ready to Learn More?
Trust Your Brand Protection to Authentix
As the authority in authentication solutions, Authentix brings enhanced visibility and traceability to today’s complex global supply chains. For over 25 years, Authentix has provided our clients with physical and software-enabled solutions to detect, mitigate and prevent counterfeiting and other illicit trading activity for currency, excise taxable goods, and branded consumer products. Brand protection is an integral component of our services.
Through our proven client partnership model and sector expertise, we offer custom solution design, rapid implementation, consumer engagement and complete program management to ensure product safety, protect revenue and maintain consumer trust and loyalty for the best global brands on the market. Contact us now to see what we can do for your brand.
Mike Consterdine, Account Development Manager for Brand, Authentix
Mike Consterdine has been involved in the Brand Protection industry for nearly 15 years, helping brands secure their products through protection and enforcement of their IP portfolio. Having worked as an external investigator for a number of global luxury and apparel brands, Mike also developed and managed the international enforcement program for a leading consumer electrical appliance manufacturer.
Using his wealth of knowledge in the field he is able to consult brand owners on best practices in anti-counterfeiting and anti-diversion programs. Representing Authentix, Mike will be able to outline how secure product marking enables authentication and traceability, whilst online to offline brand protection enables business growth.
Mike explains that Brand Protection is “a passion as well as a profession, protecting people is the reason. Whether you have counterfeiting, diversion or fraud issues, it’s key to be proactive and collaborate with your network to be successful in any Brand Protection program.”
To learn more about our brand protection solutions and how we can help you, please email Mike at Mike.consterdine@authentix.com.
Are Companies Held Liable For Fake Products?
|By the Authentix Brand Protection team
Brand protection often isn’t the first thing on a company’s mind as they launch a new product. When a company sets out to design a product, they want it to be a hit. They strive to make it useful and helpful to people, and they want their customers to trust and love the new product. Many brand owners refer to their products as their “baby” due to the long and challenging process to get it just right, in addition to the thought and testing that goes into the product research and development process.
One of the most powerful practices a company should apply to their products is often overlooked and that is brand protection, which can protect a company from unforeseen liability costs and customer mistrust in emerging or gray markets. Estimates vary, but the total amount of counterfeit goods impacting the job market is astonishing — it’s responsible for the loss of 2.5 million jobs globally.
When Brand Reputation is on the Line
An expression often used in sales states, “You are only as good as your last deal.” Similarly, brand reputation plays a significant role in the sales of most products. More than ever, customers are informed and do their research, reviewing competitors and finding the best deal according to various factors such as quality, cost, and reputation. A positive brand reputation can take years to build and only moments to collapse. (For example, in 2019, Nike pulled its products from the Amazon marketplace in part to try to lessen the damaging effects that counterfeit goods were then having on its brand). A brand’s positive reputation can be ruined due to a counterfeit product damaging someone’s skin, hair, body, or health.
Any product that is a premium brand and popular (e.g., car parts, cosmetics, pharmaceuticals, clothing, or even bed sheets) will be counterfeited at some point and can severely damage the reputation of the brand name. It can take many years and a significant amount of money in marketing and legal fees to rebuild public trust. The risk of this predicament can be materially reduced or even avoided with an investment in a brand protection program right from the start.
Forgoing Brand Protection Is Not an Option
When companies decide to forgo a brand protection program for the release of a premium product, several adverse outcomes can occur. The product may end up in non-targeted marketplaces where consumers find counterfeited or unauthorized and often heavily discounted versions. In many cases, this could also happen with brand owners’ third-party manufacturers producing unauthorized products for their own benefit.
In these cases, brand owners may also be held liable for those counterfeit products because there is little way to prove the provenance or authenticity of the fakes vs. the legitimately produced goods. For example, if a consumer in the marketplace gets hurt by an unauthorized or fake product, the brand owner is often exposed to liability. The legal fees can pile up quickly with no end in sight, all while product sales drop due to the lack of consumer trust.
In addition to counterfeited products, there is the gray market where consumers may find a company’s genuine products sold by unauthorized distributors at deeply discounted pricing, such as being sold out of the “back of the truck” or through other nonstandard channels. These may include expired or out-of-season products where the selling price is much less than the Minimum Advertised Price (MAP).
Supply Chain Physical Visibility & Traceability Simplified
Navigating a solid brand protection program does not have to be overly complex or challenging to implement. For example, putting a digital identifier or UIM on a product is much like putting a license plate on a car. That plate’s unique letter and number combinations should only be found on the exact vehicle with matching registration.
The same goes for placing a security taggant and/or a secure digital code on a product — it is only made for that specific product. The quantity and size of the product’s merchandising and packaging will determine the best security feature(s) needed to later identify the authenticity and unique attributes belonging to the product.
A covert or visible encrypted QR code with a unique, serialized item level ID can provide track-and-trace insight for a brand owner. This can provide much-needed supply chain visibility and uncover gray market diversion. If there is a question of the authenticity of a product, a consumer or inspector can check for various covert and/or overt security features (depending on the brand protection program the brand has in place).
For example, when a company’s product is entering the country of destination, the border patrol can easily detect the proper security taggants and confirm the validity of the product, allowing it to reach the distribution and retail channel much faster without delays in customs.
Online Brand Protection for Added Peace of Mind
Online brand protection is another factor to consider. If a product is sold in an online marketplace, there are tools today that can make the authentication process even easier. Many providers now have image searching and can digitally compare images for authorized licensed goods offered on non-authorized sites. Also, as part of online brand enforcement efforts, inspectors can view the product image for special overt security features to help identify these suspect products.
Today’s modern online brand protection advancements allow for identifying fake products and providing ancillary services such as cease-and-desist letters and a formal process to request site takedowns from legitimate or dark web marketplaces. Online brand protection services can perform sample buys and help find, chase, catch, and investigate infringing operators in multiple marketplaces, shutting them down and further protecting your trademark.
Consumer Engagement & Authentication Significant to Growth
For traditional core brand protection programs, the growing trend of merging consumer engagement with digital product authentication in a single platform can be insightful for a growth-minded strategy. There are many technology options for both brand owners and authentication providers in developing these hybrid and dual-purpose programs. Such services allow consumer interaction for marketing purposes while forming large data sets to detect trends as the product’s journey is tracked.
As consumers become more vigilant and seek genuine products when shopping for premium brands, including a consumer engagement feature also provides an effective means of protecting products. Moreover, it enables direct engagement with loyal consumers to help increase both customer interaction and continued brand loyalty.
The Value of Complete Brand Protection
The return on investment of implementing a brand protection program from the beginning of a product’s introduction to the market is a valuable and worthwhile investment for several reasons. It can help detect fake or unauthorized products quickly, mitigate potential liability costs that may result, and help support a brand owner’s preferred market pricing by avoiding unauthorized gray market activity. Being able to police all third-party manufacturers can also be a crucial result of a well-implemented brand protection program.
Ready to Learn More?
About Authentix
As the authority in authentication solutions, Authentix brings enhanced visibility and traceability to today’s complex global supply chains. For over 25 years, Authentix has provided clients with physical and software-enabled solutions to detect, mitigate, and prevent counterfeiting and other illicit trading activity for currency, excise taxable goods, and branded consumer products. Through a proven partnership model and sector expertise, clients experience custom solution design, rapid implementation, consumer engagement, and complete program management to ensure product safety, revenue protection, and consumer trust for the best-known global brands on the market. Headquartered in Addison, Texas USA, Authentix, Inc. has offices in the North America, Europe, Middle East, Asia, and Africa serving clients worldwide. For more information, visit https://www.authentix.com.
Footnotes
1 BASCAP, Estimating the global economic and social impacts of counterfeiting and piracy, Frontier Economics, 2011
2 Elizabeth Segran, Nike tried playing nice with Amazon. Here’s why it didn’t work, Fast Company, 2019
Tips to Avoid Online Counterfeit Products During The Holiday Season
|This year’s holiday period will bring the busiest shopping season of the year including a growing portion of purchases made online, an environment ripe for counterfeiters and scammers to take advantage of buyers by pushing fake products or phishing for personal and financial information. The consumer product counterfeit business has evolved and grown from city sidewalks to the online global marketplace. We’ve listed below a few helpful tips to be mindful of this risk and potentially avoid purchasing counterfeit products online during this high-volume and often confusing purchasing season.
Helpful Tips
1) Check to Confirm the Shopping Website is Secure.
When purchasing items online, make sure you are only purchasing from trusted sources. By verifying the website is secure, you are less likely to deal with illicit sites either selling fake products or worse, looking to steal your personal and financial information. One method to verify you are more likely to be on a legitimate site is to check the web address bar, where you’ll find the fully expressed website domain address. If a site address begins with “https://” the “s” stands for secure. You should also see a padlock symbol at the top of your browser. While this isn’t 100% foolproof, if you don’t see these indicators, chances are you have stumbled into a non-secure and possibly illicit e-commerce site.
Another tip is to be cautious of sponsored search results on Google that can lead to little-known e-commerce portals. Sponsored content which typically appears higher up in a search result or sponsored content appearing on social media that targets consumers directly are not always trustworthy. It is also recommended to be cautious of sales offered on chat apps, email campaigns and short video apps. The original website of the brand owner should normally be the first port of call, followed by the reputed e-commerce websites. On reputed e-commerce sites, use caution and evaluate the seller you’re buying from. For example, if you see a seller sell reputed brands alongside generic goods the products will most likely be fake.

2) Evaluate if the E-Commerce Site Shows the Warning Signs of Highly Discounted and Unrealistic Offers.
Many brands are often impersonated online by websites offering large price savings or special onetime deals. Be cautious of websites offering retail pricing at substantial discounts from the manufacturer’s suggested retail price. A deal that seems too good to be true probably is. Often these illicit trading sites need to use these pricing and promotional tactics to attract the web traffic and entice shoppers to navigate and purchase fake or unauthorized goods. Google Transparency Report and Scam Advisor are helpful sources to view a site’s legitimacy. We also recommend never purchasing anything online with terms of purchase not allowing returns and stating all sales are final.
Another rule of thumb to verify if the site is more likely selling legitimate product is to check the brand owner’s official, authorized website and compare the standard retail price offered on the same product against the price quoted on the questionable site. Often, discounts of 30% or more for premium branded products should be suspect. Also, check the brand owner’s official site for any mention of similar deals or a list of authorized distributors/dealers. If you’ve ordered and received product under these questionable circumstances, it is important to always inspect the products fully and compare the product’s appearance to the legitimate images on the brand owner’s site. It is also important to check all packaging, missing or expired dates or broken/non-existent safety seals. If you discover inconsistencies and suspect you’ve received a fake product, be wary of using it, especially if the failure of the product could result in your own bodily harm. It might be time to request a refund and/or report the purchase to the authorized brand owner.
3) Refer to Legitimate Verified Buyer’s Reviews as a Potential Credibility Builder.
If the shopping site you’re visiting is credible, there should be substantial and believable third-party reviews from multiple verified buyers. Make sure to browse several consumer reviews to verify the content is believable and visit other review sites such as Google My Business and Yelp to review the seller’s reputation and any negative customer experience feedback that’s already out there. Sometimes, rogue traders try to plant fake reviews with glowing praise. Thus, it may also help to sort reviews by low to high rating, and quickly check if any customer has complained of the product being substandard or even suspecting it to be counterfeit.
Many Brand Owners Work Diligently to Protect Their Brand’s Online Credibility
Authentix provides some of the world’s most recognizable brands with sophisticated online brand protection tools and services to address a broad range of online infringement and counterfeit risks. From global online surveillance and enforcement, online investigations and site takedowns, target verification, and even offline investigations, Authentix helps major brands to proactively reduce the threat of unauthorized or outright fake product hitting the online marketplaces.
If you’re a brand owner and curious how Authentix Online Brand Protection can help protect against intellectual property infringement, schedule a consultation with our brand protection experts today.