Control diversion, reduce counterfeiting and engage consumers.
By the Authentix Brand Protection Team
Preventing unauthorized products from entering the marketplace has long been a major concern and challenge for brand owners. Products determined to be at risk should be protected to prevent adverse financial impacts as well as the health and safety of the loyal consumer. In today’s more complex supply chains, deceptive practices such as counterfeiting, diversion and product tampering continue to be an unfortunate reality requiring more brand owners to take a proactive approach and implement protective measures to insure both the value of their brand investment and the safety of their customers.
Traditionally most brand owners have turned to a combination of security features including covert taggants and inks, overt specialty inks, and tamper evident closures as the most widely utilized security features to protect the higher value and most targeted products. However, other emerging technologies are enabling more choices by taking advantage of the near ubiquitous base of smartphones now estimated at over 3 billion active users worldwide. New technology is becoming available which takes advantage of recent improvements in optical imaging and digital graphics to create digitally ‘connected’ products that can be added to the security feature portfolio for even greater brand protection while providing a connection and interaction with the consumer.
A connected product enables the sharing of information in real time about the product’s journey through the supply chain, its probable location of sale, volume-based unit sales trends, and if desired, an interactive connection to the customer whether prior to or after a purchase.
How are connected products created?
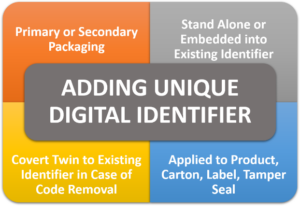
Products become digital touchpoints by adding unique, item level digital identifiers to the product or its packaging. This could include applications of a digital identifier to primary or secondary packaging; the capability to attribute or optically fingerprint an existing digital code or added as a covert digital identifier or “twin” to an existing printed code that prevents removal or copying of the code. These encrypted or covert digital identifiers can be added directly to the product carton, an adhesive multi-featured label, or a specialized tamper seal or other bottle or carton closure.
Unique identifiers can be delivered in multiple formats allowing for less complicated implementation, lower incremental costs, and increased levels of security. These may include overt or covert data matrix and QR codes, human readable alphanumeric codes, or embedded NFC chips, all of which can extend the visibility of the product’s journey from the manufacturer all the way to the retail consumer utilizing native smartphone capabilities.
Who can interact with connected products and how does it happen?
Multiple personnel can engage with a product and generate a recorded event or transaction as it moves through the supply chain to the final point of sale. These transactions, evidencing a product’s journey, may occur in different ways and for different purposes. If we split these users into three groups, these could be classified as:
- Group 1: Brand owners, vendors, employees, agents, or 3PL providers
- This group tends to use industrial scanners to engage with or interact with the codes for inbound and outbound shipments through standard supply channels
- Group 2: Contracted or agent inspector teams, law offices, law enforcement, or customs agents
- These users can validate the authenticity of a product via a smartphone, with or without an app. The addition of an app allows inspectors to impart more detailed information, such as product pedigree and interactive incident reporting and management back to the brand owner
- Group 3: End Users / Consumers
- Consumers are growing more averse to downloading proprietary mobile apps to engage with a brand and have shown a preference for QR codes and NFC tags, both functions enabled natively in most smartphones today. Therefore, the ability to simply scan the secure and proprietary code to obtain more information about the product or its authenticity is essential for a greater level of consumer participation in this process. A digital track and trace solution such as Authentix’s DigiTrax™ also supports a unique ability to tailor the consumer web experiences to company brands by enabling interactive engagement post product scan. Integrated with a single scan event, the consumer can, for instance, receive brand storytelling, digital promotions, manage loyalty programs and connect to social media channels.
Using the DigiTrax solution as an example, the digital authentication process occurs as follows:
- The user scans or taps a code on a product using a smartphone.
- The data is submitted to a secure platform which determines the authenticity of that product and the result (yes/no) is sent back to the user in real time.
- If the code is marked in the system as invalid, the user is notified, and an incident is recorded in DigiTrax.
- The user is exposed to the delivery of branded content after authentication.
- The brand owner accesses real-time scan data on a dashboard, which provides strategic insights and analytics that are helpful to multiple functional areas within the company.
How are connected products used?
Connected products are extremely powerful when used for the following objectives:
- Journey Tracking for supply chain security and operations management. This is generally used for diversion management so that supply chain personnel can see how product flows through the supply chain and if the product is in the right place at the right time. If the product is in the wrong channel or market it can then be traced back through the supply chain to determine where the diversion occurred.
- Authentication for brand protection and consumer assurance. Consumers and other users scan the product with their smart phone camera and learn whether the product is genuine or suspect. Counterfeits are revealed, and brand owners are alerted in real time with purchase locations and other critical details.

- Consumer Engagement for storytelling, branding and consumer nurturing. After authentication, consumers are invited to engage with the brand for marketing purposes. This could include receiving brand storytelling, digital promotions, loyalty and reward information, and links to social media and other brand channels.
The key to a successful brand protection program is the recognition that ROI can be achieved across multiple functions in the company and leveraging the data gleaned during the process for actionable insights and business analytics. Functions that benefit from scan data include legal, brand protection, supply chain, operations, channel management, marketing and digital engagement.
What types of data can be delivered to the brand?
An enormous amount of meaningful data can be delivered to brand owners in digital brand protection programs including information about a product’s provenance, its journey through the supply chain, the location/date/time of associated transactions including consumer scan events, validation of authentication or suspected illicit activity, and direct consumer marketing and engagement.
In summary, digital authentication and connected products are a critical component in rapid detection of product compromise and can be harnessed to deliver much more, too. Connected products are powerful inspection, reporting and communication tools that continue to deliver data to the brand and information to the consumer long after their point of sale.
To learn more about Authentix digital brand protection solutions, click here.